 If you're an experienced ethical hacker having great abilities then you may work as a freelancer by offering your companies to much organization. If you may master the command prompt in windows, then you definately is not going to only know how you can generate laptop hacking methods, but you will understand more in depth how computers really work. Just execute netstat -a and the command prompt will return a listing of computers that your laptop is linked to. 4. Now, write something to the file and it will mechanically get saved with edited date and time. 2. Now, just kind:“netsh wlan show profile” to get the checklist of all network which has been linked. While reading, I considered a few of the obstacles I've faced previously, or continue to face now, in the Elder Scrolls Online. For any queries concerning Ethical Hacking, it's possible you'll ask us by commenting beneath. It isn't attainable for me to offer acknowledgment to such tutorials and hence there have to be no copyright or legal issues concerning this tutorial.
If you're an experienced ethical hacker having great abilities then you may work as a freelancer by offering your companies to much organization. If you may master the command prompt in windows, then you definately is not going to only know how you can generate laptop hacking methods, but you will understand more in depth how computers really work. Just execute netstat -a and the command prompt will return a listing of computers that your laptop is linked to. 4. Now, write something to the file and it will mechanically get saved with edited date and time. 2. Now, just kind:“netsh wlan show profile” to get the checklist of all network which has been linked. While reading, I considered a few of the obstacles I've faced previously, or continue to face now, in the Elder Scrolls Online. For any queries concerning Ethical Hacking, it's possible you'll ask us by commenting beneath. It isn't attainable for me to offer acknowledgment to such tutorials and hence there have to be no copyright or legal issues concerning this tutorial.If that's the case that's quite frequent, search the Pc Support forums and look at the Known Issues thread. Search these forums for a huge amount of debate on the computer hack. With the passage of time, the usage of voice based mostly search is growing. Today the worldwide use of internet and other laptop network has enormously benefited the large organization in the form of sharing their information and assets and having a standard database to store their information’s. You may protect the information and folders in your laptop by utilizing this Notepad trick. Using NetBIOS for hacking is the in all probability the best option to hack remotely. These courses would assist you to to broaden your data in ethical hacking. There are various other brief term courses and workshops conducted by various institutes and organization in ethical hacking. Then there are various courses accessible in ethical hacking or internet security. With the growth of Internet across worldwide, computer security has change into a major concern for businesses and governments.
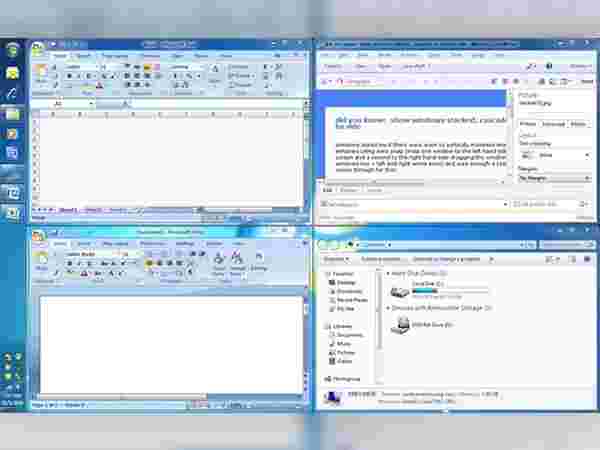
The admission to this course is based upon your computer knowledge including web servers, networking protocols, operating methods and academic background. If in case you have experience of working on a LAN using Microsoft Windows Operating Systems (like Windows98 , Windows Me, Windows NT and many others), you must have clicked on "Network Neighborhood" to access the computers attached to your network. Be certain that you have got telnet enabled on your Pc. Windows users are provided with the basic control panel to make changes to their system. As all the password or network security key will get stored or saved in windows system file, we can view it easily without Admin Access with the help of Command Prompt. This sharing of information over a computer network has also created opportunities for the malicious user to hack the system and gain access to the confidential information of an organization. Hacking is a term refers unauthorized access to a computer network or security methods of an organizations.
So here most wanted in all CMD tricks. We’re going to show you 28 tips and tricks to make your life working with Jupyter easier. Unfortunately you’ll must make the tweak manually, but we’ll walk you through it. If you are a passionate ethical hacker and have acquired great skills and can find the network flaws, weak points or vulnerabilities in a network system, then you definately could possibly be easily hired by an organization or any government agency. How one can change into a Certified Ethical Hacker? An ethical hacker is one that hacks computer networks not for anti social reasons but to let the network administrators know about the security holes so that they can prevent their computers from hacking. This site accommodates all Latest and Cool Computer tricks as well as some Internet Tricks, Registry tricks, Orkut tricks, Windows tips to customize and Optimize the performance of the system by tweaking or tricking the windows registry keys.
No comments:
Post a Comment